2014-04-11 By Stephen Blank
In 1999 two Chinese officers published a study called “Unrestricted Warfare,” arguing that war itself had changed and that it had “morphed” into a phenomenon where the principles of war were no longer Clausewitzian, i.e. the use of armed force to compel the enemy to submit to one’s will.
Instead those principles now were “using all means, including armed force or non-armed force, military and non-military, and lethal and non-lethal means to compel the enemy to accept one’s interests.”[i]
Although Clausewitz may well have successfully weathered this one of many attempts to debunk him, for it is hardly clear that they debunked his definition of war as an attempt to compel the enemy to do our will, today there can be little doubt that the forms of war we see on a global basis also correspond in many particulars to these concepts or, pace Hugo Chavez, Bolivarian war.[ii]
Today we see a global series of “unrestricted” wars, orchestrated by at least three governments, (Russia, Iran, and North Korea) all of which are clearly aimed at the US, its partners, and allies on a global level.
These wars are global and bring together states, terrorists, insurgents, bankers, high and low-ranking government, judiciary, customs, police, and security officials in many countries in loose overlapping networks that target US interests, allies, partners, or the US itself on multiple simultaneous and dynamic fronts not all of which actually involve the direct use of violence.
These forms of subversion and of unrestricted war could involve drug running, money laundering, bribery and corruption of high-placed officials, shady business deals, use of banks to evade US sanctions, e.g. on Iran, various forms of gun running, also but not necessarily in conjunction with the evasion of sanctions, e.g. North Korea, and outright support for revolution, insurgency, terrorism, civil war, and the proliferation of weapons of mass destruction using any and all of these means.
Beyond these aspects, these networks are always interpenetrated by states which in many cases are the moving spirits, i.e. the principals, behind them. In all these conflicts terrorists, organized crime, intelligence activity, criminalized business, revolutionaries, and governments all wear many hats simultaneously, making it extremely difficult to trace who is doing what, where, when, how, and why, to whom.
Furthermore the waging of unrestricted warfare comprises a Janus-faced operation in which supposedly or even actually illlicit relationships and publicly listed activities between states like arms sales and business relationships possess a second, shadow side that facilitate programs of action like weapons and drug smuggling, support for insurgencies etc.
Practicing the Art of Unrestricted Warfare
On any given day transnational threats involving two or more states or would-be states collaborating against a third party force themselves to our attention. Many, though by no means all, of these cases of transnational threats clearly represent threats against either U.S. interests or those of our allies and partners.
For example, in mid-July, 2013, Panamanian authorities discovered a North Korean ship carrying a Cuban missile and airplanes to North Korea for as yet undisclosed reasons. This cooperation, whatever its purpose, exemplifies what obviously is a well-established pattern of bilateral illicit cooperation in pursuit of strategic goals against American and allied interests, as well as a flagrant breach of a UN Security Council resolution.[iii]
But it is hardly an isolated case either for North Korea, Cuba, or for other actors in world affairs.
North Korea’s illicit activities have been well chronicled in the last few years and center on drug running, acquiring capital and technology for nuclear and conventional weapons and selling missile technology abroad for cash.[iv]
At the same time as this story broke Israeli sources reported that a report from West Point provided ample evidence for extensive government and military linkages at the highest level of Pakistan’s elite, including a director of Pakistan’s Atomic energy commission, connected to the Lashkar-e-Taiba terrorist organization.[v] And activities that are clearly traceable to Iran continue to appear.

In 2013, Nigeria, a US ally, the authorities discovered a Hezbollah armory in Kano that was intended for use against Israel and Western interests. Nigerian authorities also clearly connected this armory to its indigenous terrorist groups, among them Boko Haram.
And given Hezbollah’s dependence on Iran for arms, it is quite possible that Tehran was involved in this instance.[vi] And, in the last year Iran’s cooperation with insurgents, terrorists, and criminals, a common nexus in Latin America and Africa, is now also finally receiving the attention it deserves.[vii]
As these and other examples show today’s global threat environment involves not just governments supporting insurgents which, after all, is a centuries-old phenomenon but the actual use by governments of international criminal syndicates, insurgents, and terrorists for purposes of carrying on an unrelenting campaign of military-political subversion of targeted states.
In this type of war, which is already upon us, our adversaries often wear multiple hats, serving simultaneously as businessmen, spies, criminals, terrorists, drug runners, or government officials. Moreover they form a loose transnational network comprising members of all of these and possibly other professions.
Neither is this form of warfare limited to the DPRK or Pakistan or to Third World areas. Much of it takes place across or at least through Europe as well.
But a common denominator is that such warfare is orchestrated by one or more state for purposes of obtaining strategic advantages, often against US interests or allies.
Thus this is not simply a problem of organized crime even though crime has plagued humanity since history began and remains a threat to societies everywhere.
Rather we are dealing with activities and organizations that include the use of organized crime syndicates and organizations for the systematic corruption, disruption, and potential takeover of state power in targeted countries, including numerous forms of association with insurgents and/or terrorists.
Therefore the criminal threat transcends crime and the linkages among actual criminals or criminalized governments and their “proxies” from country to country. The threat is much greater and much more diffuse than that.
In these wars, we encounter a network of states, criminals, — drug traffickers, traffickers in people and raw materials that are in one way or another contraband — including possibly nuclear or nuclear-related materials, conventional weapons and technologies for them, money laundering and classical espionage involving the acquisition of intelligence and the compromising of prominent people or those with access to key assets and information – insurgents, terrorists, spies, corrupt officials, and “businessmen” who moonlight as both spies and criminals.
The purposes of such operations not only entail the strengthening of these insurgent and/or criminal, terrorist groups, but also the subversion of governments, often the subversion of governments friendly to the U.S. In other words this is a form of what has been called asymmetric and/or political warfare carried on by networks.
The Russian Case
Russian, Iranian, and North Korean activities are simultaneously not only criminal in nature but also are strategic operations undertaken in pursuit of a national interest aiming at weakening the position of the US and its allies across the globe.
Arms transfers, up to and including technologies and parts needed for weapons of mass destruction, are a particularly dangerous example of this kind of war. For example, Russia’s controls over the missiles and other weapons that it has sold to Syria and Iran also proved to be remarkably porous as many of them went to Hezbollah in 2000-2006 and probably since then as well.[viii]
And Syria’s chemical warfare arsenal to a large degree originated in Russia or the Soviet Union.[ix] And there is good reason to believe that there is much hardware going to dangerous states from Russia through third parties or other unaccountable middlemen.
Already in July, 2000 Kommersant reported that:
The world community has long treated Belarus as a sickly child, of whom few demands are made, that had previously been exploited by Russia, which under U.S. pressure had to abandon direct cooperation in the military sphere with Iran.
Russian military-industrial complex output started reaching the Iranians via our Belarusian brothers, who had few commitments to Washington [and this was during the Gore-Chernomyrdin agreement’s operation-author] Cooperation between Minsk and Baghdad has been developing rapidly of late.
Official statistics confirm that Belarusian-Iraqi trade turnover in 1999 came to $6million.
According to Kommersant’s information, that indicator was understated at least 10-fold.[x]
Obviously this form of gunrunning occurs in the Middle East, Latin America, and Africa as well. Iran’s ties with Russia offer an even more dangerous example of what happens when the arms sales business becomes enmeshed with high-level corruption leading the criminalization of state policy.
The 2009 incident of the Arctic Sea, a ship that reportedly left Russia and was supposedly hijacked by pirates in the Baltic Sea and disappeared until the Russian Navy tracked it down in the Cape Verde Islands illustrates how the cancer of corruption in the arms trade infected Russian arms sales to Iran.

More and more it looks like this ship was chartered to run Russian missile parts to Iran, indicating an extensive network of corruption throughout the arms sales and military industrial complex establishments.
Allegedly the Mossad discovered this sale and tipped off Russian intelligence so as not to embarrass Russia.[xi] But this situation embodies the dangerous link between the Russian arms mafia and the government, including corrupt officials and middlemen.
As an Israeli columnist wrote at the time:
In modern-day Russia, there really does exist a symbiosis between the state and the weapons mafia.
In this situation, the mafia does not always have to act in circumvention of the state machine to supply weapons to pariah states.
The mafia — and this might be the most important conclusion to be drawn from the story of the disappearnce of the notorious freighter (Arctic Sea-author) – – can be used as a weapon for state policy.
Clearly, the Rusisan government will not dare use official channels today to supply missile systems to Iran.
However, when it is the mafia at work, illegally selling these systems, well, what can the government do when it is certain that merely lumber is being exported from the country?[xii]
Even more serious charges surfaced later in a report by the leftist forum.msk.ru newspaper. It alleged that the Russian government, operating through the GRU led by General Valentin Korabel’nikov, put together a decade-long program of clandestine weapons sales to Iran after 1998 to keep Israel and Washington guessing as to Iran’s true capabilities.
This gray and black market program also enlisted the cooperation of the governments of Algeria and Syria, the arms brokers Viktor Bout and Munzer al-Kassar (who was arrested in Spain in 2007 and since extradited to the United States), and Russian organized crime figures in Spain, along with members of the PKK who have bases in Iran and engage regularly in arms trafficking.
In other words, Moscow orchestrated a long-running program of illicit and clandestine arms sales to Iran, involving terrorists, insurgents, criminals, and complicit governments until the network began to break down with the arrests of the Kurdish contact Zakhar Kalashov, thanks to the efforts, among others, of Anatoly Litvinenko who was murdered in 2006, probably by Russian intelligence.
That initial arrest led to other arrests, the breakup of the program, Algeria’s return of Russian weapons, allegedly because they were defective, the sacking of General Korabel’nikov, the break up of the network with the arrests of the two arms brokers, and an abortive last attempt, using the Arctic Sea to run weapons to Iran in 2009.[xiii]
If these reports are true they would represent the depths of corruption to which the arms trade has brought the Russian government in its linkages with organized crime, linkages that are also a fact of life in the government’s energy business, and illustrate the dangers this trade poses to Moscow and to international security more generally.
But they would also perfectly exemplify the networked scope and significant transnational reach of such operations involving governments, bankers, criminal syndicates, insurgents if not terrorists, arms sellers and suppliers, shipping organizations, customs officials, etc. in a host of countries.
Since Iran then re-exports these weapons, including possibly Shahab-3 missiles, to other rogue states like Syria or terrorist groups this amounts to playing with fire.[xiv] This urge to play with fire and also to be on both sides of the action in the Middle East is not new.
We have seen it earlier in Iraq. Before the invasion of Iraq in 2003 Russia simultaneously sought partnership with Washington, a free hand at home and in the CIS against terrorists, and friendship with Iraq. It was prepared to look the other way if Washington took account of Russian interests in Iraq, more broadly the Gulf, and the CIS because those interests were both economic and political and because they served to enrich key political elites in Moscow and validate Russia’s stance as a legitimate actor regarding Iraq’s destiny beyond Russia’s membership in the Security Council.
Those interests included large debts of $7-8 Billion, large-scale energy contracts to develop Iraqi oil fields, large-scale trade in Russian goods under the notoriously corrupt oil for food program that, as we now know, enriched many members of Russia’s top elite.
Beyond that the Gulf states in general were and are regarded by two of Russia’s most prominent lobbies after energy, defense industry and the Ministry of Atomic Affairs (Minatom), as fertile hunting grounds for large profitable sales.[xv]
At the same time Russian intelligence was furnishing Saddam Hussein with the results of Western conversations about Iraq and running weapons to Iraq, again indicating Moscow’s desire to keep a foot in both camps.[xvi]
Meanwhile for over a decade probably until 2010, Moscow had been the main provider of external support for Iran’s missile, air defense, space, and navy programs.[xvii] This cooperation went back a long way. In 1998 Yevgenia Albats outlined Russo-Iranian collaboration in helping Iran build nuclear missiles for use as a future IRBM to target Israel and Turkey.
Iran also hopes to build an ICBM to target the United States and Europe. Albats detailed the conscious participation and coordination of Russia’s Federal Security Service (FSB), the State Commissions on Non-Proliferation, and on Science and Technology, Yevgeny Primakov’s Ministry of Foreign Affairs, and probably the Ministry of Defense in projects to send Russian scientists to Iran to transfer nuclear know-how as Iran aims at IRBM’s and then ICBMs.[xviii]
The large number of Russian scientific-technological institutions helping Iran develop its programs strongly suggests governmental involvement in coordinating this interaction, especially as many of them either have close connections with the government, or are under its authority, or claim to have informed the government of what they were selling to Iran.[xix]
The known technology transfers of WMD to Iran involve production technology and testing of the rocket engine for the SS-4 missile in violation of the MTCR, the reactor at Bushehr, as well as the continuing exchange of scientific know-how with Iranian scientists and/or training in Russia for them.[xx]
The Key Elements of Unrestricted Warfare
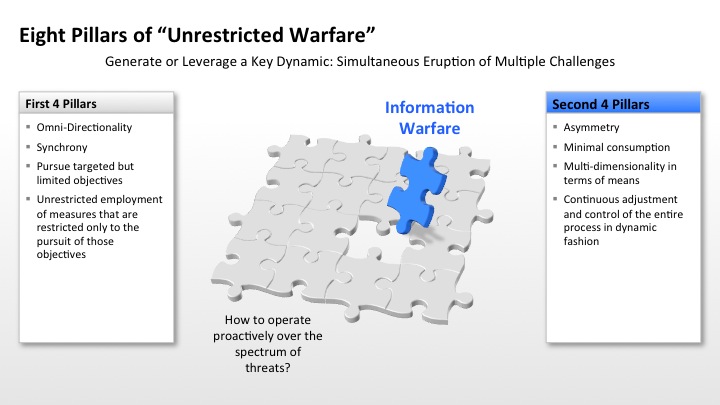
Unrestricted warfare, according to its Chinese authors has eight pillars.[xxi]
The first pillar is that this form of warfare takes place globally or on a 360-degree observation and design and utilizes all forms of kinetic and non-kinetic defense capabilities and factors. The financing and support of crime, addiction, corruption, arms transfers, illegal smuggling, and the corruption of public and governmental institutions across the globe certainly matches with this requirement.
This “omni-directionality,” to use the authors’ term, eliminates distinctions between what is and is not the battlefield in pursuit of strategic advantages.
Using IT and the other tools of the trade, purveyors of this warfare essentially have taken the Leninist solution of using Socialist movements and ramified Communist party political and military organizations as surrogates for the lack of an organized or capable army to a new level.[xxii]
Every conceivable avenue of approach is therefore sanctioned, as this war knows no restrictions. And thus wars of these kinds encompass the entire network of a society’s relationships.
The second pillar is synchrony, actions taking place at the same time across the depth of the entire “theater”. All the activities described here are ongoing and occurring globally. But they can ideally be orchestrated or turned on and off like a rheostat as circumstances in any particular theater warrant.
For instance, principals could decide at any given time to elevate the crisis in Latin America while downgrading support for insurgencies in Africa or vice versa.
The third pillar is limited objectives. The aim is not to destroy the US and its military or government or necessarily those of any other state but rather to weaken them and prevent their ability to restrict the aggressor’s activity. The goal is to keep the level of provocation below that threshold (unless necessary) where the targeted state might lash out and destroy the network in his country or Russian, Chinese or DPRK capabilities altogether.
Nevertheless in targeted Third World areas the cumulative impact of these operations over time is to destabilize or even take over the targeted states if not entire regions around them, e.g. Colombia.
The fourth pillar logically follows that in pursuit of the limited objectives that are within the reach of the active network waging this kind of war and within that framework of limited goals the attacking force should pursue “unlimited measures.” This entails the unrestricted employment of measures that are restricted only to the pursuit of those objectives.
For Chinese writers Sherman’s march to the sea represents a burn and plunder operation that shunned actual combat in order achieve a limited objective of attacking the South’s will and capacity to fight without giving battle. That exemplifies an unlimited measure in support of a limited objective.[xxiii]
The fifth pillar is asymmetry, operations conducted in ways contrary to enemy expectations or understanding of the balance of symmetry. The breadth and scope of the operations described in these papers certainly lend themselves to that kind of asymmetric operations since their initiators now command not only a global reach but also a diverse global portfolio of capabilities with which to conduct their operations anywhere in the world.
The sixth pillar is minimal consumption.
What this means is waging this war with the least necessary expenditure of resources. And as we know from our own bitter experience this translates into a cost-imposing strategy, e.g. the minimal cost of the Al-Qaida 9/11 operation vs. the huge costs of Afghanistan not to mention Iraq.
The orchestrators of these kinds of operations, whether they be in Moscow, Tehran, Caracas, Pyongyang, or elsewhere have within their capability the means to (or they may so believe) to launch similar cost-imposing crises against the US in “peripheral areas” that Washington and its allies must nonetheless spend time, money, and men to defend while they can initiate them at minimal cost.
The seventh pillar, which flows from the foregoing pillars, is that of multi-dimensionality, namely the coordination and allocation of all forces, military and otherwise, that can be mobilized, to accomplishment of the task at hand and realization of the objective in question.
This entails coordination and cooperation among all kinds of forces in different spheres, e.g. the coordination of partisan with regular army warfare on the Eastern Front in World War II.
Lastly the eighth pillar is the continuous adjustment and control of the entire process in dynamic fashion, using all the instruments of warfare as conceived here and of national power towards accomplishment of the objective.[xxiv]
Information Warfare (IW) is a key aspect of unrestricted warfare.
IW in this context does not refer primarily to the disabling of physical infrastructure, e.g. electricity grids, power plants, etc. like the well-known Stuxnet virus used against Iran’s nuclear program but rather, as defined by Russian and Chinese authorities alike to a much broader concept.
For example, in 2009, First Deputy Chief of the Russian General staff, Alexander Burutin stated that IW is not only essential in disabling command control structures (C2) of military establishments but more importantly:
The essence of contemporary information attacks lies in altering the outside principles of societal structure and the life of society with the help of information expansion.
This can be done by imposing onto the citizens moral norms and cultural traditions that are foreign to them.
Unfortunately, so far, our efforts have been directed at the defense of separate vial facilities, at a time when we have to be constructing a correlated information defense system.[xxv]
Similarly Chinese military forces have been trained since 2003 in what China calls Public Opinion Warfare, “a concept that seeks to support combat operations efforts by strengthening public support, demoralizing foes, and building international support through innovative tactics employing mass media.”[xxvi]
In other words, this form of IW, like unrestricted and strategic hybrid warfare, recognizes no limits to the scope of its activity. The entire socio-economic-cultural-political-informational-military space of the targeted country is fair game.
Not only do Russian and Chinese strategists believe that IW or one or another form of this political warfare (also using IW), they believe that this is US strategy and is being used against them.[xxvii]
Worse yet, incautious American analyses claiming that we employed such a strategy to effectuate regime change in Serbia in 2000 will only lend further credence to such views.[xxviii] Thus the “takeaway” point here is that their analysts now believe (if ours do not they will say we still practice this strategy) that regime change in unfriendly states can be accomplished through largely non-violent means, or a combination of these low-level forms of violence, plus subversion, and IW as described here.
Indeed, some Russian analysts maintain that this is how we took down the Soviet Union.[xxix] Accordingly in discussing these eight pillars we must always remember that they are being deployed simultaneously and in tandem with IW as part of an overall strategic approach.
Shaping an Approach to Compete in an Age of Unrestricted Warfare
It should be noted that the capabilities of the US and its allies to deter armed conflict has led as well to adversaries shifting to focus on a broadened concept of war which is suggested by the unrestricted war concept.
The recent military actions by Russia in Ukraine are the operational outreach of an unrestricted war concept, whereby the goal is to use the armed forces to re-shape the strategic environment in your interest through chess moves, rather than directly confront the adversaries military might. The goal is to erode, not confront, and then whittle away with the use of armed force where feasible.
The Russian actions in Georgia and Ukraine are clear examples of building in military intervention tools into a broader strategic mosaic.

For the US Armed forces as a whole and the government there are several lessons that may be drawn from the assertion and practice of unrestricted warfare.
First, we are facing multiple overlapping adversaries and networks.
Cuba’s links to both North Korea and Russia exemplify the kind of loose, overlapping relationships involved. But the multi-national aspects described in the papers here involving arms sellers, bankers, customs and airport officials, etc. in many different countries all of whom play a part in facilitating such activities throughout the world.
While a plan of action may originate in Moscow, Tehran, Pyongyang, or potentially Beijing; it can be carried out through these intermediaries in a host of locales and ramped up or down as the situation, seen from the principals’ vantage point, warrants.
Second, accordingly we may liken these threats to rheostats that can adjust temperature up or down as needed.
While the framework of operations is always in a state of latent if not manifest readiness, the scale of the threat can be adjusted higher or lower in one or more location as the situation calls for.
This could lead to the simultaneous eruption of multiple challenges to us and our allies and partners in multiple locations.
And these multiple challenges can range from classic military challenges to indirect pressure points as well.
Third, the challenges we face are multifaceted and blend the classic military with a much wider range of tool sets. They can range from the Russian use of energy revenues, tied to criminal activities to subvert European governments from the Baltic to the Black Sea, to gun running in the Balkans and Caucasus to the activities described above to the kinds of transactions made by North Korea and Syria, etc., to actual military operations in selected theaters, or to sustained IW operations as described by Russo-Chinese writers or campaigns like that in Serbia to unseat Milosevic.[xxx] Or then to armed intervention into states that are susceptible to map change, such as Georgia or Ukraine.
Consequently and fourth, the nature of the US response demands an entirely new approach.
Under the long-term conditions of fiscal and manpower restraint that we will be operating under, in each country what is required is first of all a genuine “whole of government approach.” The military will often play, if anything, an input role to be combined with members of organizations like the FBI, DEA, the Treasury Department, intelligence agencies, the Coast Guard, police organizations, and advisory teams of the appropriate military services in the host country.
Stovepipes must be ruthlessly broken, information shared, action coordinated laterally as well as vertically, and genuine country teams must be permanently in action. Moreover, those teams or our own and allied networks must often act proactively since we now live in what analysts call a risk society where we may not be able to specify a direct, linear process between cause and effect.
Risks are often unknowable, submerged, and latent but not visible and adversarial behavior is much less predictable or even deferrable. Therefore we must often act or at least be ready to act in a proactive and precautionary fashion.[xxxi]
Moreover, and fifth, given the constraints upon us due to manpower, fiscal, and political restrictions in host countries, more often than not it is likely that the main role played by the U.S. military will be one of advising and training, as part of the preparation for the support of allies and partners in dealing with a multiplicity of threats.
The US military in all of its services, at least in peacetime, must adopt an operational concept that emphasizes security cooperation as a means to both deter potential adversaries from striking at US partners and to forestall war rather than to deter by means of operations that are not easily conceivable because it cannot mount long-range strikes on its own, except in limited cases.
Indeed, the Navy-USMC team already embraces the idea of enhanced security cooperation to forestall and deter wars even as it is steadily moving to implement its air-sea battle concept.
As CNO Admiral Jonathan Greenert has tated,
The Navy-Marine Corps team provides the nation offshore options to deter, influence and win in an era of uncertainty.
Our naval forces are at their best when they are forward, assuring allies and building partnerships, deterring aggression without escalation, defusing threats without fanfare, and containing conflict without regional disruption.
We keep the Fleet forward through a combination of rotational deployments from the United States, Forward Deployed Naval Forces (FDNF) in Japan, Guam and Italy, and forward stationing ships in places such as Bahrain or Diego Garcia.
Our ability to operate forward depends on our U.S. bases and strategic partnerships overseas that provide ―places‖ where the Navy-Marine Corps team can rest, repair, refuel and resupply.[xxxii]
Finally our role should be preventative, i.e. we, operating with our partners and allies must aim to nip threats in the bud and forestall them rather than let them grow into full-fledged insurgencies, civil wars, etc.
We must understand that not only are unrestricted or strategic hybrid warfare globally conceived forms of unending positional warfare directed against us, but also that these wolves have long since been at the door and that such warfare occurs now on a global basis in multiple formats but with the overarching strategic aim of weakening us and our allies and partners.
Shaping an interactive and integrated capacity to deal with a set of cascading means to reshape the map and to undercut our interests is the task for the next decade of the 21st century.
Dr. Stephen Blank has written and analyzed the Russians and other strategic players for many years. Currently, he is a Senior Fellow American Foreign Policy Council, Washington DC.
Editor’s Note: The key role of exercises and training is well understood by key parts of the US military and we have written frequently about the centrality of this role in shaping a distributed strategy in the Pacific, or deterrence in depth.
https://sldinfo.com/black-sea-rotational-force-marines-come-to-latvia/
https://sldinfo.com/the-usmc-shift-in-the-pacific-and-the-role-of-exercises-a-marforpac-perspective/
https://sldinfo.com/flipbooks/SPMAGTF/Special%20Purpose%20MAGTF%20Crisis%20Response/
And earlier Douglas Farah provided a multiple part series on the role of various global networks in shaping a challenging strategic environment for the US and its allies:
https://sldinfo.com/emerging-alliance-criminalized-states-and-terrorist-criminal-pipelines/
https://sldinfo.com/emerging-alliance-criminalized-states-and-terrorist-criminal-pipelines-part-ii/
https://sldinfo.com/emerging-alliance-part-iii/
https://sldinfo.com/emerging-alliance-part-iv/
https://sldinfo.com/emerging-alliance-part-v/
https://sldinfo.com/emerging-alliance-part-vi/
https://sldinfo.com/emerging-alliances-for-the-21st-century-part-vii/
[i] Ibid, p. 7
[ii] Max G. Manwaring, Venezuela as an Exporter of 4th Generation Warfare Instability, Carlisle Barracks, PA: Strategic Studies Institute, US Army War College, 2012; Idem: Latin America’s New Security Reality: Irregular Asymmetric Conflict and Hugo Chavez, Carlisle Barracks, PA: Strategic Studies Institute, US Army War College, 2009: Idem. Venezuela’s Hugo Chavez, Bolivarian Socialism, and Asymmetric Warfare, Carlisle Barracks, PA: Strategic Studies Institute, US Army War College, 2005; Douglas Farah, Carlisle Barracks, PA: Strategic Studies Institute, US Army War College, 2012
[iii] Rick Gladstone, Gerry Mullany, and Choe Sang-Hun, “Panama Seizes North Korea-Flagged Ship for Weapons,” New York Times, July 16, 2013, www.nytimes.com
[iv] Sheema Chestnut, “Illicit Activity and Proliferation; North Korean Smuggling Networks,” International Security, XXXII, No. 1, Summer, 2007, pp. 80-111, Raphael Perl, “Drug Trafficking and North Korea: Issues for U.S. Policy,” Congressional Research Service Report for Congress, 2007; Liana Sun Wyler and Dick K. Nanto, “North Korean Crime-for-Profit Activities,” Congressional Research Service Report for Congress,, 2008
[v] Open Source Center, OSC Summary, in English, July 1, 2013, www.opensource.gov
[vi] “Nigeria: Hezbollah Armory Discovered in Kano City,” BBC News, Africa, www.bbc.co.uk/news/world-africa-22722948?print=true, May 30, 2013
[vii] Cynthia J. Arnson, “Testimony by Cynthia J. Arnson, Director, Latin American Program
Woodrow Wilson International Center for Scholars, Before the Senate Foreign Relations Committee, Subcommittee on the Western Hemisphere, Peace Corps, and Global Narcotics Affairs, “Iran’s Influence and Activity in Latin America”, February 16, 2012; Douglas Farah, “Testimony of Douglas Farah, Senior Fellow, International Assessment and Strategy Center, , Before the Senate Foreign Relations Committee, Subcommittee on the Western Hemisphere, Peace Corps, and Global Narcotics Affairs, “Iran’s Influence and Activity in Latin America”, February 16, 2012; Roger Noriega, “Testimony of Ambassador Roger F. Noriega,
Thursday, Before the Senate Foreign Relations Committee, Subcommittee on the Western Hemisphere, Peace Corps, and Global Narcotics Affairs, “Iran’s Influence and Activity in Latin America”, February 16, 2012; Ilan Berman, “Iran’s Influence and Activity in Latin America, Testimony Before the United States Senate Committee on Foreign Relations Subcommittee on Western Hemisphere, Peace Corps, and Global Narcotics Affairs, February 16, 2012; Ilan Berman, “Testimony Before the House of Representatives Homeland Security Committee, Subcommittee on Oversight and Management Efficiency,” July 9, 2013; Cynthia Arnson, Haleh Esfandiari, and Adam Stubits, Eds., Iran in Latin America: Threat or ‘Axis of Annoyance,’, Woodrow Wilson Center Reports on the Americas, No. 23, Washington, D.C.: Woodrow Wilson Center , 2012 are just some of these assessments
[viii] Andrew McGregor, “Concerns Mount Over Hezbollah’s Rearmament,” Jamestown Terrorism Focus, III, No. 38, October 3, 2006; Iason Athanasiadis, “How Hi-Tech Hezbollah Called the Shots,” Asia Times Online, September 9, 2006; Mikhail Barabanov, “Russian Anti-Armor Weapons and Israeli Tanks in Lebanon,” Moscow Defense Brief, NO. 4 (10) 2007, “Russia Denies Supplying Hezbollah with Missiles,” Radio Free Europe Radio Liberty Features, August 25, 2006
[ix] Janis Bruehl, “Where Did Syria’s Chemical Weapons Come From,?”Propublicahttp://www.propublica.org/article/where-did-syrias-chemical-weapons-come-from; James Brooke, “Russia Helped Build Syria’s Chemical Weapons,” The Moscow Times, September 11, 2013, http://www.themoscowtimes.com/opinion/article/russia-helped-build-syrias-chemical-weapons/485870.html
[x] Moscow, Kommersant in Russian, July 19, 2000, FBIS SOV, July 19, 2000
[xi] “’Israel Link’ In Arctic Sea Case,” BBC, September 9, 2009, http://news.bbc.co.uk/2/h/europe/8247273.htm
[xii] Vitaly Portnikov, “The Phantom Ship and a Living Mafia,” Tel Aviv, Vesti-2 Supplement, in Russian, September 10, 2009, FBIS SOV, September 10, 2009
[xiii] “Global Alternative: The Logical conclusion of a major Failure of Russian Intelligence,” Moscow, www.forum.msk.ru, in Russian, November 9, 2009, FBIS SOV, November 9, 2009
[xiv] Jerusalem, DEBKA-Net Weekly Internet Version, in English, July 21, 2006, FBIS SOV, July 21, 2006
[xv] Ariel Cohen, “Russia and the Axis of Evil: Money, Ambition, and U.S. Interests”; Eugene B. Rumer, “Russia’s Policies Toward the Axis of Evil: Money and Geopolitics in Iraq and Iran,” Testimony to the House International Relations Committee, February 26, 2003,wwc.house.gov/international_relations/108/rume0226; Celeste A. Wallander, “Russian Interest in Trading With the “Axis of Evil”, Ibid., www.house.internatonal_Relations/108/wall/0226
[xvi] David Harrison, “Revealed: Russia spied on Blair for Saddam,” The Daily Telegraph, April 13, 2003, www.telegraph.co.uk
[xvii] Alexander Nemets and Steffany Trofino, “Russia: Tipping the Balance in the Middle East,” Journal of Slavic Military Studies, XXII, NO. 3, July, 2009, pp. 367-382; Alexander Nemets and Robert W. Kurz, “The Iranian Space Program and Russian Assistance,” Journal of Slavic Military Studies, XXII, NO. 1, 2009, pp. 87-96
[xviii] Moscow, Novaya Gazeta Ponedelnik, in Russian, March 16-22, 1998, Foreign Broadcast Information Service, Arms Control, (Henceforth FBIS TAC) 98-076, March 17, 1998
[xix] Kenneth Katzman, “Iran’s Long-Range Missile Capabilities,” REPORT of the COMMISSION TO ASSESS THE BALLISTIC MISSILE THREAT TO THE UNITED STATES, July 15, 1998 Pursuant to Public Law 201, 104th Congress, Appendix III, Unclassified Working Papers, pp. 198-199, David Fillipov, “What US Calls Arms Proliferation, Russia Firm Calls Business as Usual,” Boston Globe, August 19, 1998, p. 1
[xx] Moscow, Komsomolskaya Pravda, in Russian, October 22, 1997, FBIS TAC, 97-295, October 23, 1997
[xxi] Qiao Liang and Wang Xiangsui; LTC. William T. Hagestad, II, USMA, (RET), 21st Century Chinese Cyberwarfare, Rolling Meadows, IL: IT Governance, 2012, pp. 56-61
[xxii] Stephen Blank, “Class War on the Global Scale: The Culture of Leninist Political Conflict”, Stephen J. Blank Lawrence E. Grinter, Karl P. Magyar, Lewis B. Ware, Bynum E. Weathers, Conflict, Culture & History: Regional Dimensions, Maxwell AFB, Al.: Air University Press, 1993Conflict, Culture, and History: Regional Dimensions, Air University Press: Maxwell AFB, Alabama, 1993, pp. 1-55
[xxiii] Hagestad, pp. 56-61. We need not agree with this assessment of Sherman’s march to understand what the Chinese authors are driving at. The accuracy of their perceptions is not the issue here. Rather it is the nature of that perspective which is of importance.
[xxiv] Ibid.
[xxv] Moscow, Svobodnaya Pressa, in Russian, March 17, 2009, FBIS SOV, March 17, 2009
[xxvi] Open Source Center, Analysis, “PLA Refines Study, Practice of ‘Public Opinion Warfare,’ FBIS SOV, November 17, 2008
[xxvii] Stephen Blank, “Information Warfare a la Russe,” Paper Presented to the Conference: Cyberspace: Malevolent Actors, Criminal Opportunities, and Strategic Competition, Ridgway Center of the University of Pittsburgh,” November 1-2, 2012; Timothy Thomas, China’s Cyber Incursions: a Theoretical Look At What They See and Why They Do it Based on a Different Strategic Method of Thought,” Paper Presented at GSPIA-SSI Conference on Information Warfare, University of Pittsburgh, Pittsburgh, PA November 1-2, 2012
[xxviii] Gregory L. Schulte, “Regime change Without Military Force: Lessons From Overthrowing Milosevic,” Prism, IV, No. 2, Summer, 2013 pp. 45-56
[xxix] Blank, “Information Warfare a la Russe”; Thomas
[xxx] Schulte, pp. 45-56
[xxxi] Yee-Kuang Heng, “Reflexive Rationality and the Implications for Decision-Making,” Heidi Krkinen, Ed., Strategic Decision-Making in Crisis and War, Helsinki: National Defense University, Department of Strategic and Defense Studies, Series 2 Research Reports No. 42, 2010, pp. 25-29
[xxxii] Admiral Jonathan Greenert. “Statement of Admiral Jonathan Greenert ,Chief of Naval Operations Before the Congress on FY 2013 Department of Navy Posture, March 2012, http://www.navy.mil/cno/120316_PS.pdf, p. 8

